Ever had the need to load a Comma Separated Values (CSV) file in PHP? This simple code block will do it quickly.
Continue reading “Simple CSV loading in PHP”Blog
Customise the Laravel User Verification email
Starting with Laravel 5.7, the framework has updated the User and Auth models to include an email verification contract.
While this is very straightforward to initially configure, customising the content of the emails sent is not so obvious.
Continue reading “Customise the Laravel User Verification email”Deploying Cockpit on Debian – Part 3
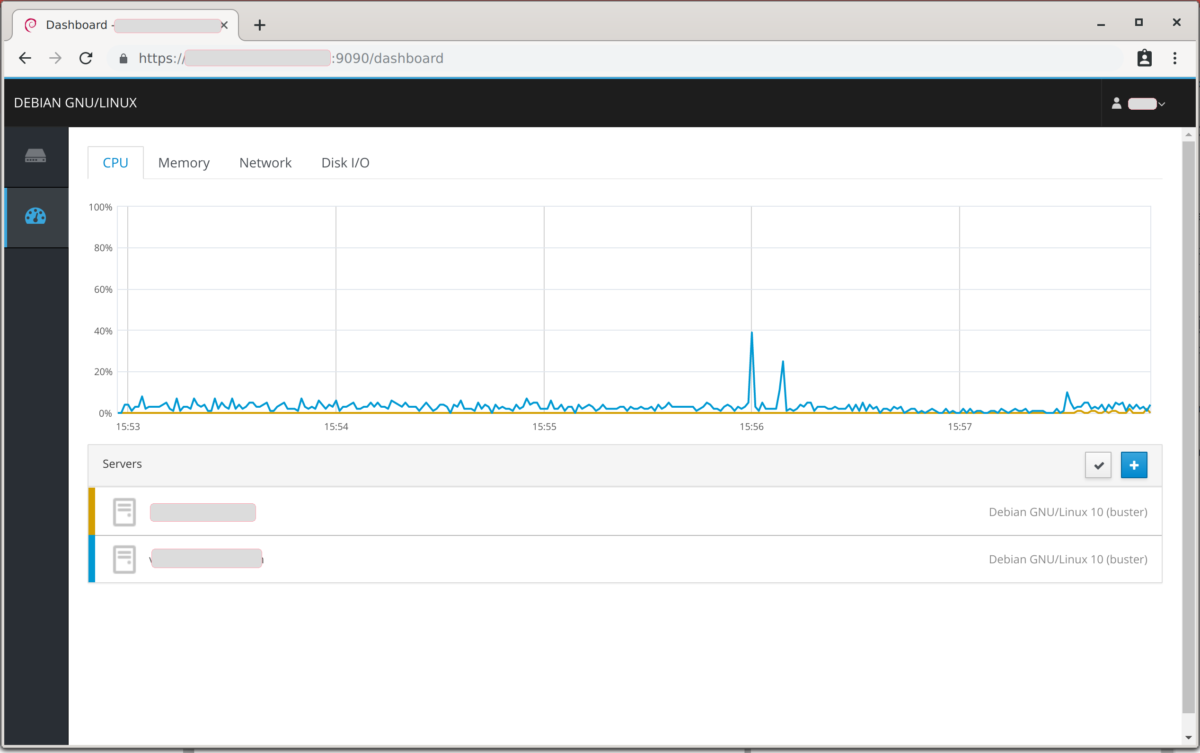
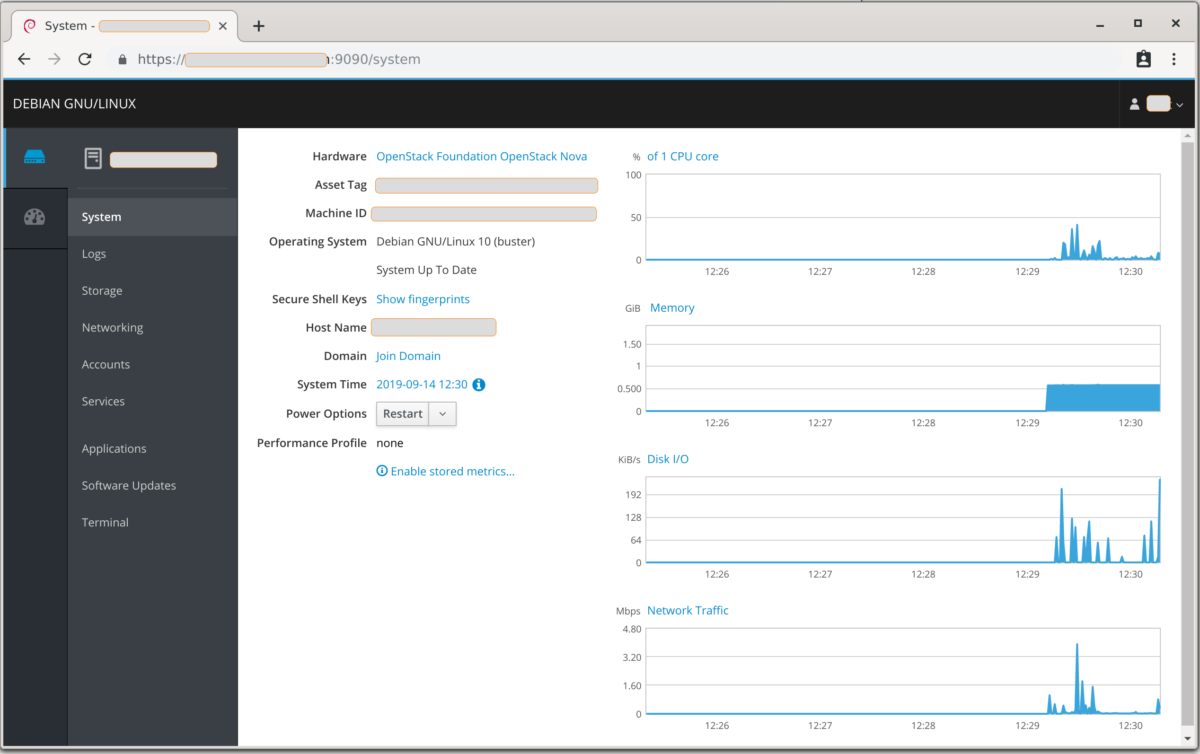
In the first two parts of this tutorial we looked first at the initial setup and configuration of Cockpit, then how to add additional hosts.
In this third and final part, we shall put Cockpit behind a reverse proxy.
Continue reading “Deploying Cockpit on Debian – Part 3”Configuring fail2ban on Debian – Part 2
In part 1 of this tutorial we looked at installing fail2ban and configuring some of the default jails. In this second part we shall look at some further jails, and configure filters and jails for applications not covered by the default installation.
Continue reading “Configuring fail2ban on Debian – Part 2”Using a Yubikey for 2-factor authentication
For those of you who have not yet encountered a Yubikey, it is a physically small security key which empowers passwordless or 2-factor authentication in a number of different scenarios. They now support a huge number of protocols including One Time Passwords, NFC, FIDO2, U2F, Smart card, and OpenPGP.
Mine has been living on my keyring for several years now, and has proved invaluable for me accessing both my physical and electronic world.
Continue reading “Using a Yubikey for 2-factor authentication”Creating first user in Laravel
Laravel has some great functionality to seed databases, but they are designed primarily to be used in development and testing environments. That is not to say that they cannot be leveraged for use in production.
There is, however, an easy and quick way to create models in the production environment to get you started.
Continue reading “Creating first user in Laravel”Deploying Cockpit on Debian – Part 2
Last week, we looked at installing and configuring Cockpit on a single host. In Part 2 of this tutorial series, we shall look at how to add a second (or more) hosts so they are all visible from the original instance.
Continue reading “Deploying Cockpit on Debian – Part 2”Configuring fail2ban on Debian – Part 1
If you are administering a Linux server on a publicly accessible IP address then you have no-doubt already noticed your log files filling up with repeated failed login attempts against all common protocols. While it may be possible to protected services to some extent with firewalls, nothing is going to protect you from weak password policies and software vulnerabilities.
There is, however, a great Open Source product that can do away with some of the noise and frustrate the spammers; fail2ban.
Continue reading “Configuring fail2ban on Debian – Part 1”